Selective Access
Sovereign precision for applied AI operations.
AIBX LTD builds institutional-grade AI infrastructure with an editorial standard of clarity, control, and discretion.
- Focus
- Operational AI
- Coverage
- AIOps + Cyber Intelligence
- Jurisdiction
- United Kingdom
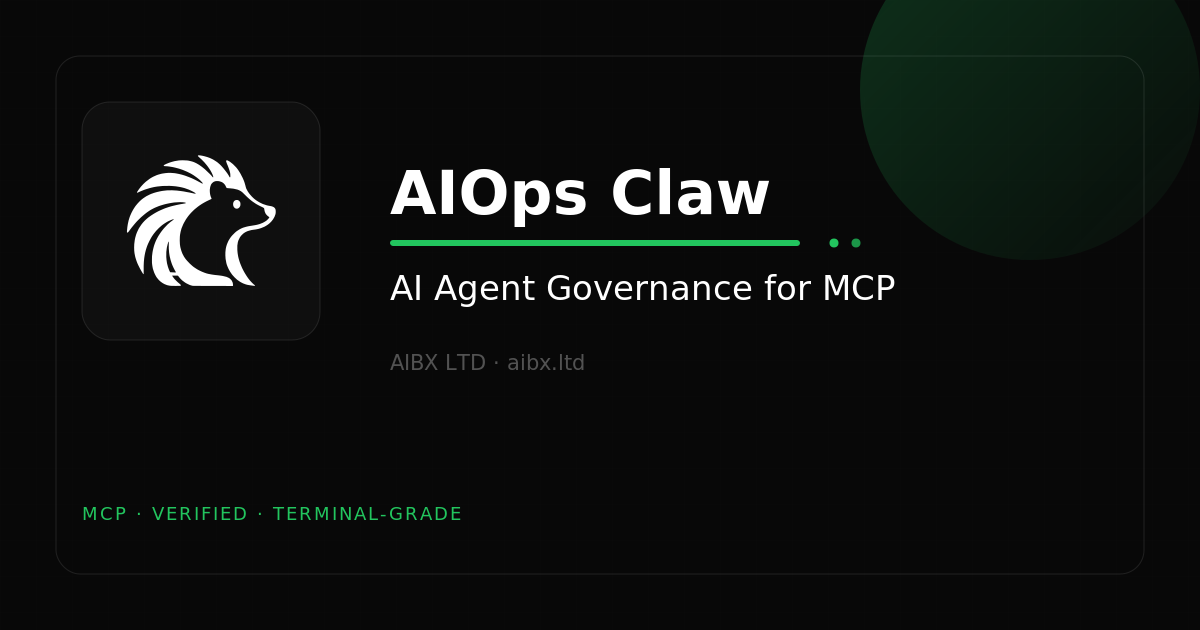
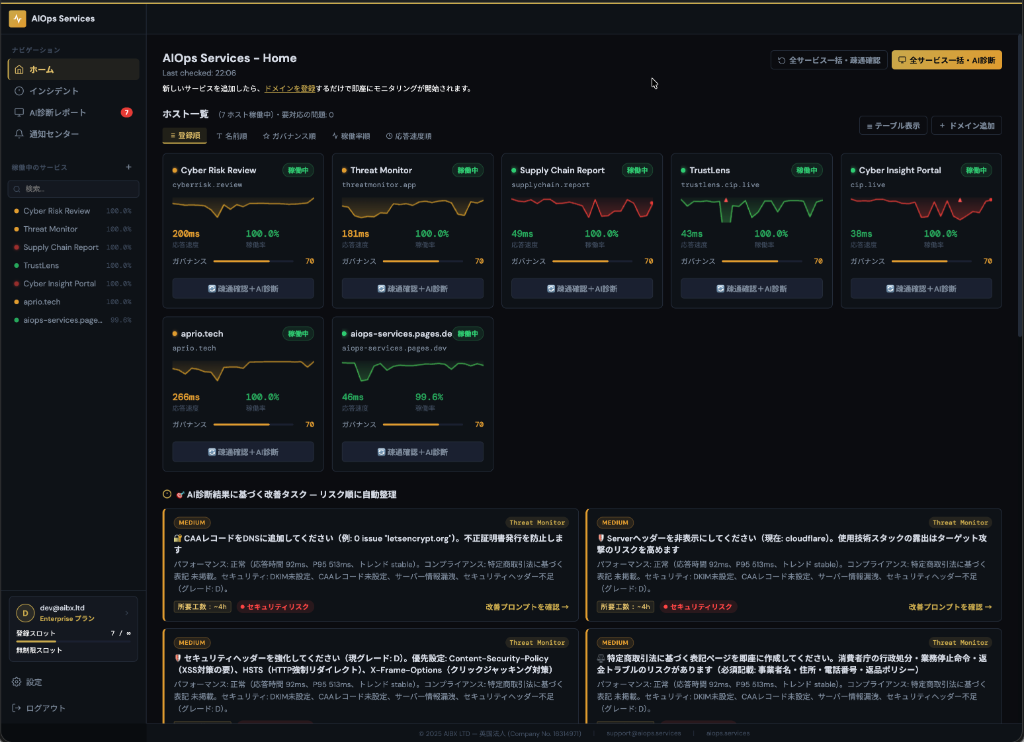
AIOps Services
AIOps Live
Real-time monitoring of AI service health with automatic generation of improvement prompts when anomalies are detected. The reliability assurance layer.
- AI service health monitoring at 5-minute intervals
- Instant detection of outages, latency, and quality degradation
- Automatic generation of improvement prompts
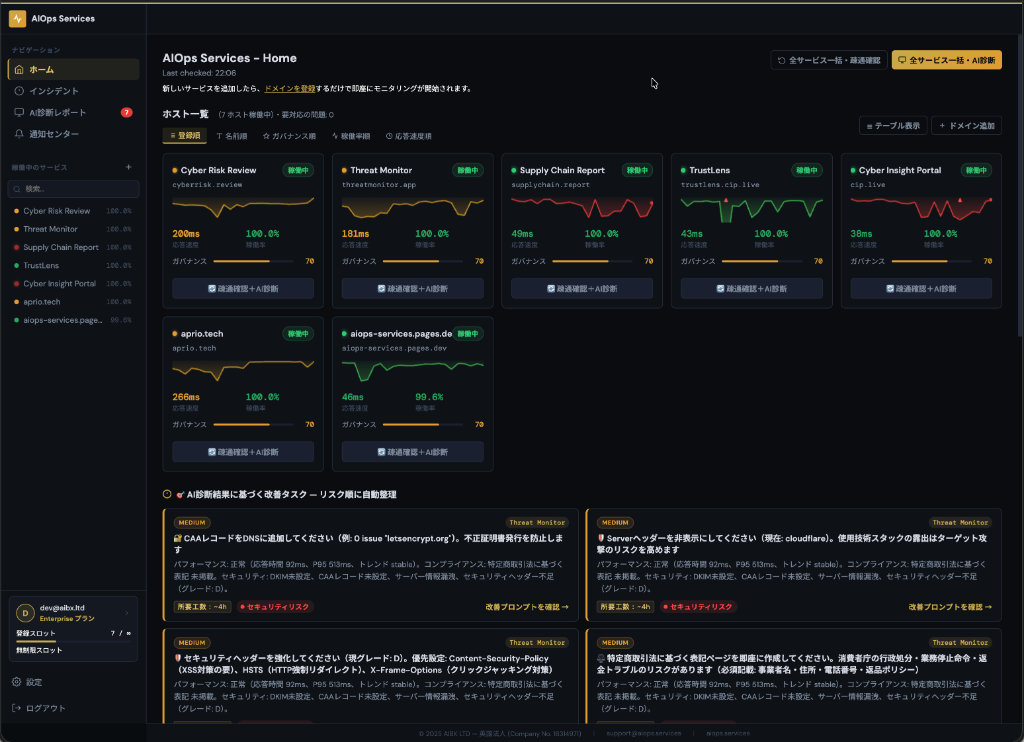
AIOps Services
AIOps Rail
MCP-native guardrail infrastructure that enforces agent behavior boundaries. 16 MCP tools for session management, approval flows, and deploy protection.
- MCP-native AI agent guardrails
- Behavior boundary enforcement via Constitutional Constraints
- Deploy integrity verification via Deploy Guard
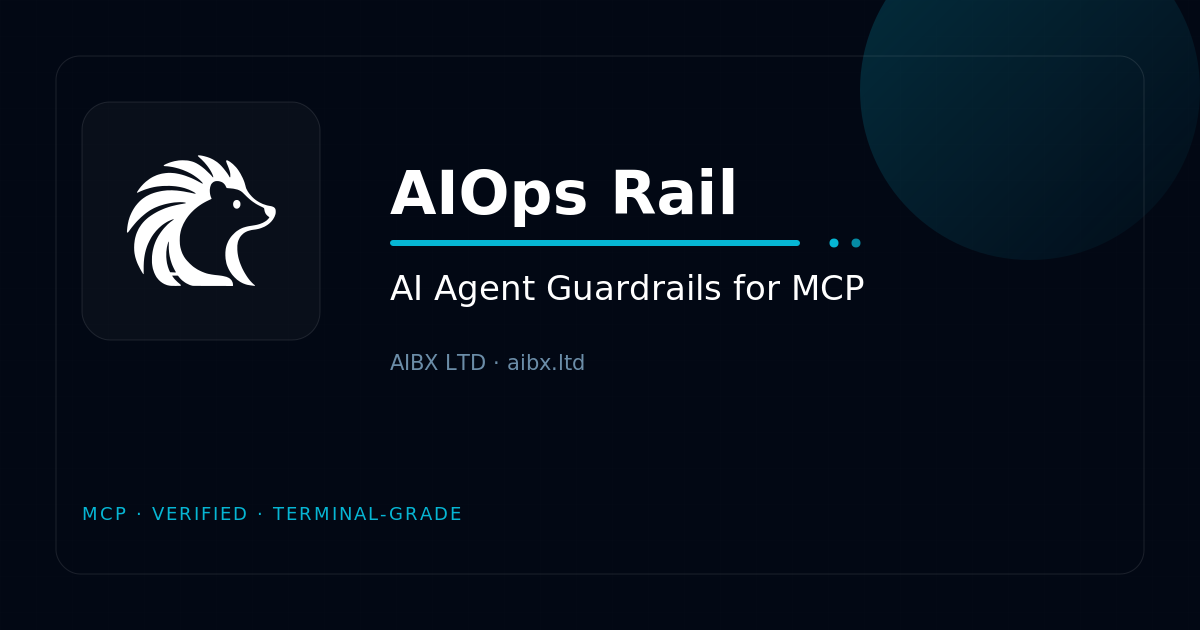
AIOps Services
AIOps Claw
Governance control plane for AI agents you build and operate. Embeds policy-as-code, pre-execution validation, and audit logging through MCP endpoints.
- Secure external tool connectivity for AI agents
- Automatic llms.txt and MCP endpoint publication
- Build-time AI agent governance
AIOps Services
AIOps Pulse
AI-powered log analysis across cloud platforms. Automates anomaly detection and operational alerting for real-time observability.
- Log monitoring for Cloudflare, Vercel, Supabase, and more
- AI-driven anomaly pattern detection
- Operational alerts with Slack integration
Cyber Risk Intelligence
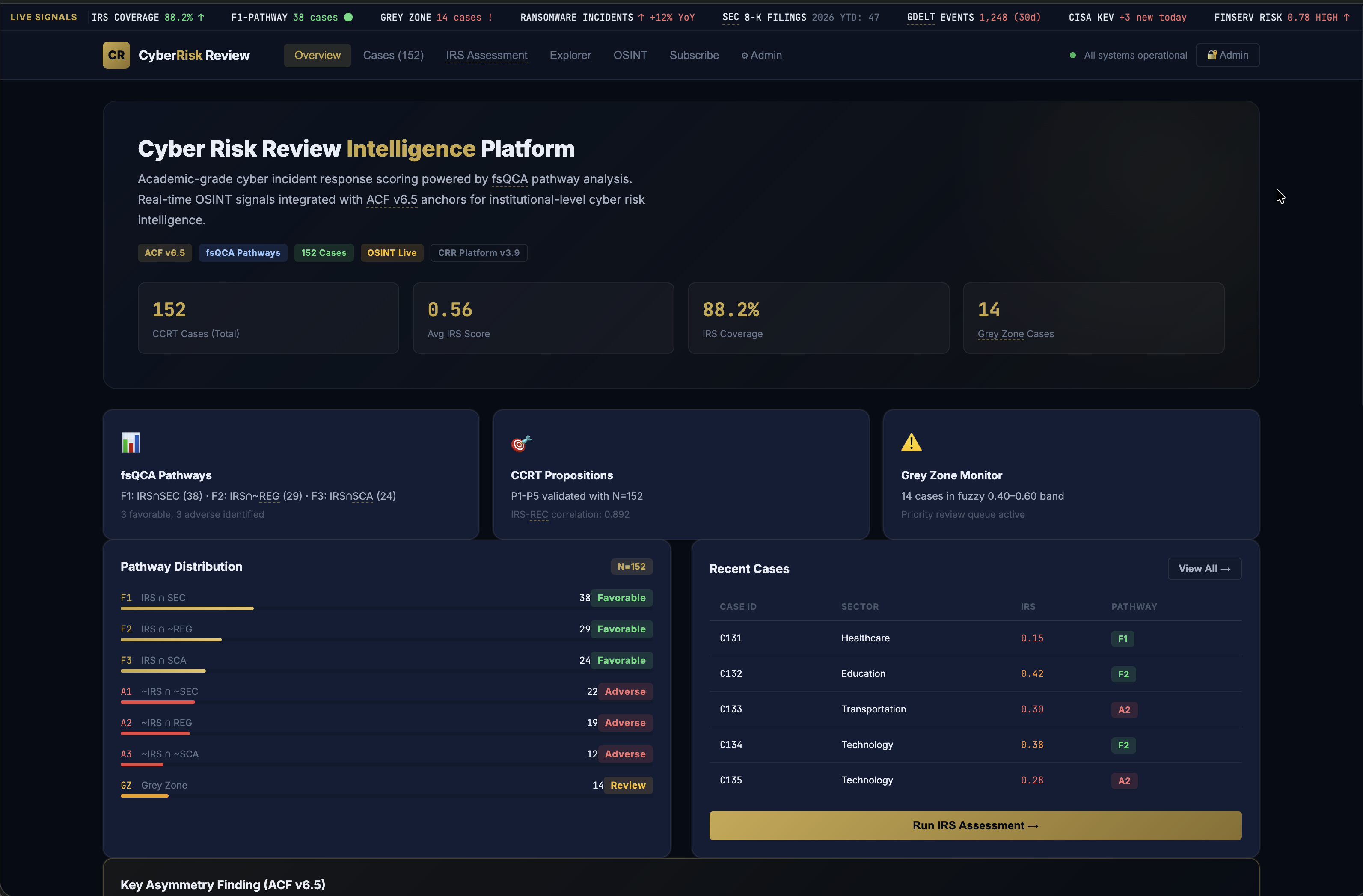
Cyber Risk Review
Continuous cyber risk intelligence for decision-makers who need disclosed-event monitoring, sector context, and structured risk visibility.
- Cyber event and disclosure tracking
- Institutional risk monitoring workflows
- Structured signals for executive review
Authority
Selective mandate.
AIBX LTD is a UK-registered company developing applied AI products and infrastructure for institutional use cases, with a focus on operational resilience and cyber intelligence.
Engagements are intentionally scoped. Public-facing products are complemented by tailored advisory and implementation support.
Registered in England and Wales
Proprietary architecture
Built for signal clarity, controlled workflows, and institutional-grade presentation.
Secure Channel
Start an enquiry.
Access requests, partnerships, and product discussions are accepted only through the secure enquiry form below.
Submission protocol
Private intake
Messages are processed through a server-side submission route and are not exposed as a public email address on the website.
- Institutional access enquiries
- Partnership and advisory discussions
- Product and media requests